Sql Injection Tool Free Download
Best Free and Open Source SQL Injection Tools. Published on October. Domain query and full SQL injection scan. Download Safe3 SQL injector tool from the.

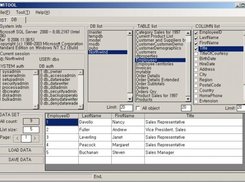
Sql injection tool free download. Hibernate Hibernate is an Object/Relational Mapper tool. It's very popular among Java applications and. Havij SQL Injection Havij is an automated SQL Injection tool that helps penetration testers to find and exploit SQL Injection vulnerabilities on a web page.The power.
• Full support for MySQL, Oracle, PostgreSQL, Microsoft SQL Server, Microsoft Access, IBM DB2, SQLite, Firebird, Sybase, SAP MaxDB, HSQLDB and Informix database management systems. • Full support for six SQL injection techniques: boolean-based blind, time-based blind, error-based, UNION query-based, stacked queries and out-of-band. • Support to directly connect to the database without passing via a SQL injection, by providing DBMS credentials, IP address, port and database name. • Support to enumerate users, password hashes, privileges, roles, databases, tables and columns. • Automatic recognition of password hash formats and support for cracking them using a dictionary-based attack. • Support to dump database tables entirely, a range of entries or specific columns as per user's choice.
The user can also choose to dump only a range of characters from each column's entry. • Support to search for specific database names, specific tables across all databases or specific columns across all databases' tables. This is useful, for instance, to identify tables containing custom application credentials where relevant columns' names contain string like name and pass. • Support to download and upload any file from the database server underlying file system when the database software is MySQL, PostgreSQL or Microsoft SQL Server.
• Support to execute arbitrary commands and retrieve their standard output on the database server underlying operating system when the database software is MySQL, PostgreSQL or Microsoft SQL Server. • Support to establish an out-of-band stateful TCP connection between the attacker machine and the database server underlying operating system. This channel can be an interactive command prompt, a Meterpreter session or a graphical user interface (VNC) session as per user's choice. • Support for database process' user privilege escalation via Metasploit's Meterpreter getsystem command. Refer to the for an exhaustive breakdown of the features. You can download the latest.
Preferably, you can download sqlmap by cloning the repository: git clone --depth 1 sqlmap-dev • sqlmap. • around sqlmap presented at conferences. Watch more demos. All code contributions are greatly appreciated.
First off, clone the, read the carefully, go through the code yourself and an email if you are having a hard time grasping its structure and meaning. Bug reports are welcome! Please report all bugs on the. Our preferred method of patch submission is via a Git.
Download Old Flash Player Windows Xp Sp3. Each patch should make one logical change. Please follow the existing stylistic conventions: wrap code to 76 columns when possible. Ford Travelpilot Nx Europe 2013 Dvd. Amtlib.dll Premiere Cc 2017 on this page. Avoid tabs, use four space characters instead. Before you put time into a non-trivial patch, it is worth discussing it privately. Many have contributed in different ways to the sqlmap development.
You can be the next! Sqlmap is the result of numerous hours of passionated work from a small team of computer security enthusiasts. If you appreciated our work and you want to see sqlmap kept being developed, please consider making a to our efforts via to donations@sqlmap.org. We also accept Ƀitcoins to 1AUrrKYsamBEThdruYTQmUfMfLF7aaxU6x. Copyright © 2006-2017 by and. All rights reserved. This program is free software; you may redistribute and/or modify it under the terms of the as published by the; Version 2 (or later) with the clarifications and exceptions described in the.